Protecting Data Centers

21st Century Utilities
With the exponential growth of data usage across various industries, data centers are responsible for safeguarding highly sensitive and confidential data. Protecting these important facilities and their reputations from targeted sabotage or criminally motivated attacks is paramount.
We specialize in the design, engineering, and management of total perimeter security solutions that protect data centers against physical breach attempts.
Crash-Rated Protection
Our range of crash-rated solutions include wedges, static and retractable bollards, gates as well as barriers. Installed with a stand-off distance or integrated with perimeter fences, crash-rated barriers harden the entire perimeter and high-risk areas within the facitlity against hostile vehicle attacks and accidental damage.

Delay possible intrusions
As part of our perimeter solutions, we work with the leading fencing manufacturer in the industry to complete our design. Betafence is known for its quality and stoic approach to delivering protection through its high-security products.
Their range of welded mesh fences is proven to delay breach attempts, an important consideration when choosing your perimeter fence. The fence must delay perpetrators long enough for security response teams to get there and stop the intrusion before they are successful.

Accurate situational awareness
Being warned about a possible threat, and knowing exactly where it might happen is essential to pro-actively protect any premises.
Integrating surveillance technology into our total solution from the beginning delivers not just accurate situational awareness, but also reduces design, engineering, civil and total project costs.
From our global partners, we source and integrate components that are best suited to each security situation.
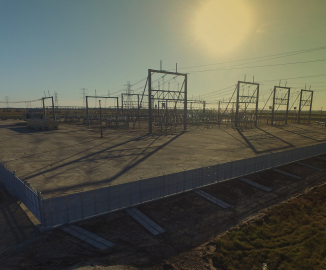
Protecting power supply
Uninterrupted power is of great importance to keep coolers going and technology up and running. We have extensive experience in protecting electricity infrastructure from malicious attacks and have assisted utility providers in complying to security regulations.